CodeSec by Contrast brings the fastest and most accurate scanner on the market right to developers for free. By packaging the same scanning engine used in our Contrast Security platform into a simple command-line interface (CLI), CodeSec empowers developers to scan, secure, and ship their code in minutes. We created this guide to not only show developers what CodeSec can offer, but to also give them the tools to test it so they can see for themselves just how fast, accurate and seamless CodeSec can be!
UPDATE: CodeSec Scan - JavaScript Client-Side Coverage has landed. Try it now!
CodeSec Delivers
- From start to finish in minutes: Frictionless and seamless signup process with GitHub or Google Account. – from zero to secure in less than 5 minutes.
- The Fastest and most accurate scanner in the market: Delivers up to 10x faster scan rates. Recognized as the fastest and most accurate Java scanner in the market.
- Immediate and actionable results: Find 70% more critical vulnerabilities, and actionable results with 6X more true positives in seconds.
CodeSec Features
CodeSec offers the following capabilities through a simple command line interface (CLI):
- NEW | CodeSec - SCA: Secure vulnerable libraries (in Java, Javascript, Python, Ruby, GO, PHP, .NET) in OSS with lightning speed, accurate scans (SCA), and actionable remediation guidance to ship code faster and create standardized SBOMs with ease.
- CodeSec - Scan: Optimize code security for Java, Javascript and .NET applications with fast, industry-leading (SAST) scans and actionable remediation guidance, in a simple command line interface. Additionally, developers can secure GitHub pipelines with Contrast GitHub Actions for free.
- CodeSec - Serverless: Take advantage of a new ground-breaking application security tool for serverless environments in Amazon Web Services (AWS) Lambda Functions (Java + Python) that detects cloud-native vulnerabilities quickly and accurately while providing actionable remediation guidance in a simple command line interface (CLI).
Test it out!
1. FINDING SAMPLE PROJECTS
You may not have access to a source code project, or if you do, your project may not have any vulnerabilities. If so, we’ve got you covered!
- Our Static Analysis Security Testing (SAST) engine operates on Java, .NET WebForms and plain client-side JavaScript code. Try the following suggestions for projects that are deliberately vulnerable:
- Java: The scan takes place on a built binary: .jar or .war files. Try the official WebGoat releases from https://github.com/WebGoat/WebGoat/releases.
- .NET: The scan tool supports WebForms and processes a built .exe file or .zip. Try a build of WebGoat for .NET. Try an official WebGoat release tailored by one of our Contrast experts here WebGoat.Net.zip
- Client-side JavaScript: The scan tool supports native JavaScript code with additional supporting in (Angular, React, jQuery, and Vue.JS) frameworks and processes a .JS file or a zipped collection of files in .zip format. Try the tailored zip folder below, created by one of our Contrast experts here Dsrc.zip
- Our SCA solution operates on Java, .NET, JavaScript, Python, Ruby, PHP and GO. If you don’t have an application you can use https://github.com/Contrast-Security-OSS/demo-nodegoat. Alternatively try one of your own projects! Our prerequisites are:
- Java: pom.xml and Maven build platforms including the dependency plugin. Or build.gradle and gradle dependencies or ./gradlew dependencies must be supported
- .NET framework and .NET core: MSBuild 15.0 or greater and a packages.lock.json file
- Node: .package.json and a lock file (either .package-lock.json or .yarn.lock)
- Ruby: gemfile and gemfile.lock
- Python: pipfile and pipfile.lock
- Go: go.mod
- PHP: composer.json and composer.lock
2. INSTALL
- Open a command-prompt or terminal, then install with NPM, Homebrew or Artifactory.
- If already installed, then choose from the following commands:
- npm install -g @contrast/contrast
or
- brew tap contrastsecurity/tap
brew install contrast
3. AUTHENTICATE
- Once Contrast is installed on your terminal, it’s time to authenticate with your GitHub or Google account by entering the following command:
- contrast auth
- Once this command is entered, a new tab in your browser will open, asking you to connect with either your GitHub or Google Account.
- Once connected, your terminal will update and you are now ready to start scanning!
4. START SCANNING
Once authenticated, enter command contrast help to see what capabilities CodeSec offers:
- CodeSec SCA - Use the contrast audit command to run a SCA scan. This enables users to secure open-source libraries and create SBOMs to manage supply-chain risk.
Once the command is entered. CodeSec will automatically search for a suitable file for SCA analysis.
Once the analysis is complete, results are categorized by severity. Vulnerable dependencies are identified, and remediation advice on the version to which to update is provided.
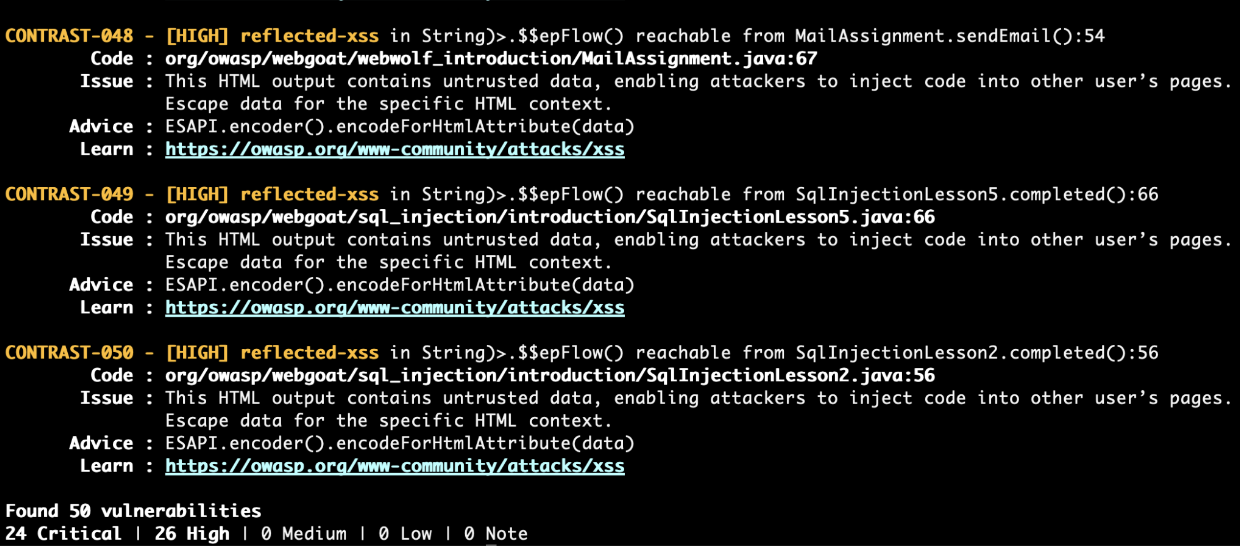
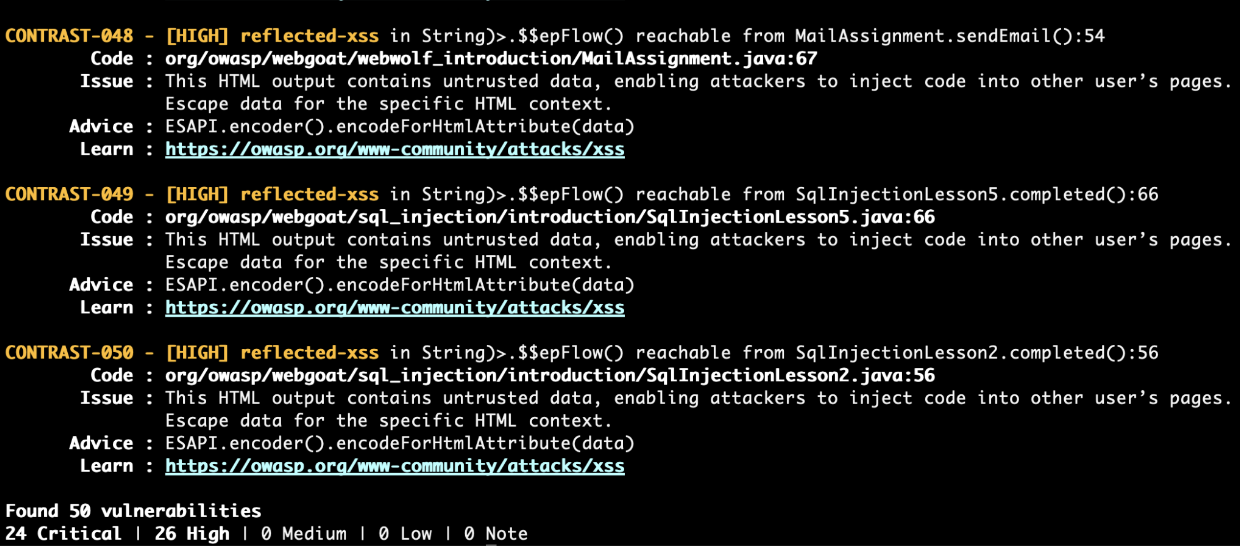
- CodeSec Scan - Use the contrast scan command to run a SAST scan. CodeSec is recognized as the fastest and most accurate Java scanner in the market. Contrast will search for suitable files to scan, or you can use -f to specify a file:
Once a scan is complete, results are categorized by severity (from Critical to Low) with actionable guidance to help developers understand what the vulnerability is and how to fix it.
- CodeSec Serverless - CodeSec supports scanning Java and Python lambda functions. To run a lambda scan, ensure AWS credentials (AWS_DEFAULT_REGION, AWS_ACCESS_KEY_ID, AWS_SECRET_ACCESS_KEY) are configured in your local environment. Then you are ready to use the contrast lambda command to scan your AWS Lambda functions.
Once a scan is complete, results are categorized by vulnerability type with actionable guidance to help developers understand what the vulnerability is and how to fix it.
More exciting features are coming to CodeSec this fall!
To learn more about CodeSec and all its updates, click here.