“Serverless” is becoming a buzzword in the application world for good reason. The term refers to a cloud-native development model that allows organizations to build and run their applications without the burdens of physical server infrastructure. Serverless applications can deliver automatic scalability, high availability, and improved business agility. This dynamic flexibility helps save time and money across the entire software development life cycle (SDLC). Serverless adoption in the enterprise has seen a 209% increase in average weekly invocations over the last 12 months. By next year, 25% of application developers are expected to be using serverless technologies due to their many advantages.
Serverless application security, however, remains a serious issue. Traditional application security testing (AST) tools cannot provide adequate coverage, speed, or accuracy to keep pace with the demands of serverless applications. It should be no surprise that concerns about configured or quickly spun-up cloud-native (serverless or container-based) workloads have increased by nearly 10% over the last year.
The Current Gap Between Serverless and Security
While serverless environments present some advantages when it comes to security, there are also some unique challenges:
- Attack surface. Every function, application programming interface (API), and protocol in a serverless application presents a broader potential attack vector.
- Porous perimeters. The boundaries of serverless applications are naturally more fragmented than traditional applications—and therefore harder to secure.
- Greater complexity. Multiple permissions and access issues can be challenging and time-consuming for organizations to manage.
Because legacy AST tools were not designed for the unique nature of serverless applications, they cannot provide fast or accurate testing results. Legacy AST tools have poor visibility into serverless architectures due to “no-edge blindness”—functions don’t have a public-facing endpoint or URL. Abstraction of the infrastructure, network, and virtual machines provides zero context for traditional tools to reference. This reduces the accuracy of testing results—upwards of 85% of alerts turn out to be false positives. And while some vendors may tout static scans for serverless applications, scanning code with zero context is not a true or effective serverless AST solution.
Using traditional AST solutions for serverless applications also requires complex evaluation and tuning by security experts—which slows down deployment. Security testing operations may also require manual intervention by security and development teams—triage and analysis of results due to high rates of false-positive alerts. These barriers make it very difficult for traditional application security tools to scale with the rigorous demands of serverless development processes.
Purpose-built Security for Serverless Applications
To actualize the intended benefits of serverless applications, organizations need purpose-built application testing that is both fast and accurate. Contrast Serverless Application Security offers a purpose-built solution for serverless application monitoring that ensures accurate testing results without the legacy inefficiencies that delay release cycles. Organizations gain full security visibility for AWS Lambda functions with near-zero false positives.
This new addition to the Contrast Application Security Platform uses context-based static and dynamic engines to automatically detect vulnerabilities within serverless environments. It helps developers easily validate and prioritize alert test results for quick, guided remediation—improving operational efficiency of serverless security by 50% while accelerating development release cycles.
Contrast Serverless Application Security—Solution Features
Contrast’s solution maps all the resources within the serverless environment, executes static code scans, and simulates tailored dynamic attacks. It automatically validates and prioritizes test results with accuracy that eliminates false positives and alert fatigue that plague traditional application security approaches. Specific solution capabilities include:
- Dynamic environment scanning. Automatically initiates tailored, dynamic security assessments based on any specific updates introduced to the tested environment in real time. This greatly improves the ease of pentesting versus legacy manual approaches.
- Resource map. Automatically discovers and presents a visualized graph of all resources (e.g., S3 bucket, API Gateway, DynamoDB) and their relationships within tested environments in a few short minutes per session. This helps security teams quickly identify weak spots and potential risks.
- Code scanning. Automatically executes assessments of relevant code and configurations to discover new vulnerabilities in near real time with context-rich remediation guidance and without manual help.
Contrast Serverless Application Security targets critical vulnerabilities such as:
- Least privilege. The solution suggests a tailored least-privilege policy for each Lambda based on its actual needs. This addresses identity and access management (IAM) vulnerabilities (over permissive functions) within serverless workloads prior to deployment.
- Custom code. Contrast detects custom code vulnerabilities and provides developer-friendly remediation recommendations.
- Open-source Software (OSS). Contrast’s unique open-source security engine performs software composition analysis (SCA) of open-source libraries.
Deployment and Management
Contrast Serverless Application Security can be deployed without the need for burdensome upfront configuration. It takes only a few minutes to get up and running, with immediate full results provided.
Contrast’s solution is deployed simply as another AWS Lambda function by connecting Contrast TeamServer to the organization’s AWS Lambda environment. To manage the solution and view results, the Contrast platform’s “Serverless” tab includes five different screen views: Functions, Scans, Results, Graphs, and Settings.
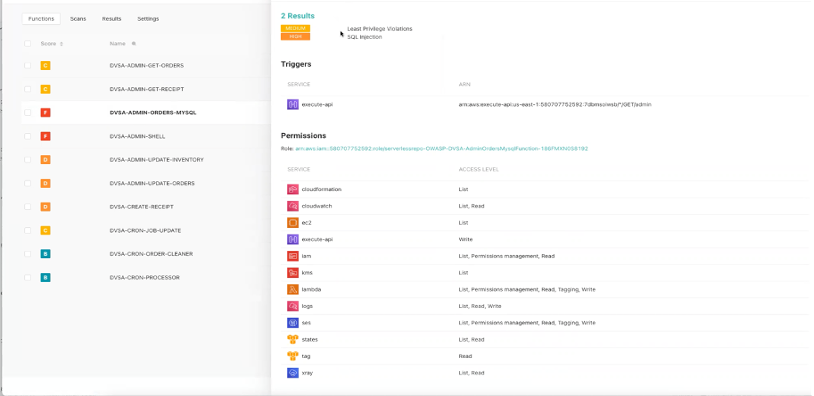
Functions. Contrast Serverless Application Security inventories each of the different AWS Lambda functions that make up the application. The left “score” column shows an assigned letter grade (A to F) that rates relative security based on scan findings together with the likelihood and potential impact. This is achieved through Contrast’s context-based engine that not only considers the vulnerability but also how the cloud configuration of the function affects the overall severity.
Clicking on any individual function listed opens detailed results with specific prioritized scan alerts, any associated service triggers (such as a dependent API), and a list of relevant permissions for that function. It also lists any AWS Tags and a graded Posture Score summary for both the parts and the whole of that specific Lambda function. These details can help developers isolate critical problems that need to be remediated.
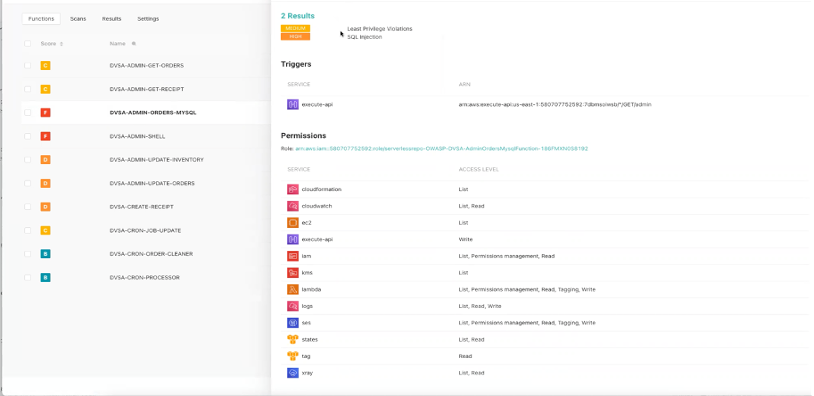
Contrast Serverless “Functions” shows detailed per-function summaries
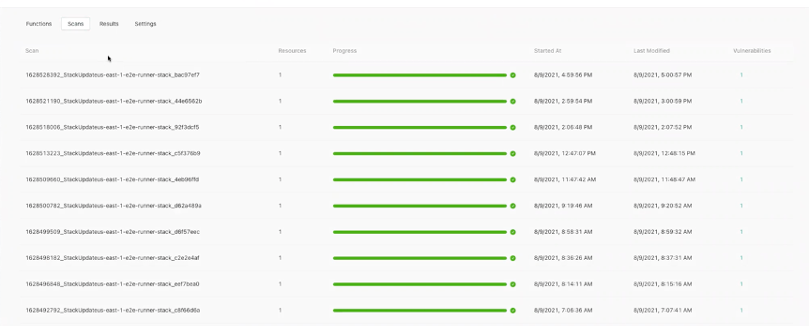
Scans. The solution keeps a historical list of all executed scans performed on the application (including those that are currently running). Each individual scan record contains a list of all scanned resources.
Contrast’s approach to serverless application security happens seamlessly in the background as part of the development pipeline. After the solution’s initial scan establishes a baseline of all the different functions, Contrast Serverless Application Security automatically tracks all future changes as developers write and revise their code. This continuous monitoring eliminates the need to stop and run new scans.
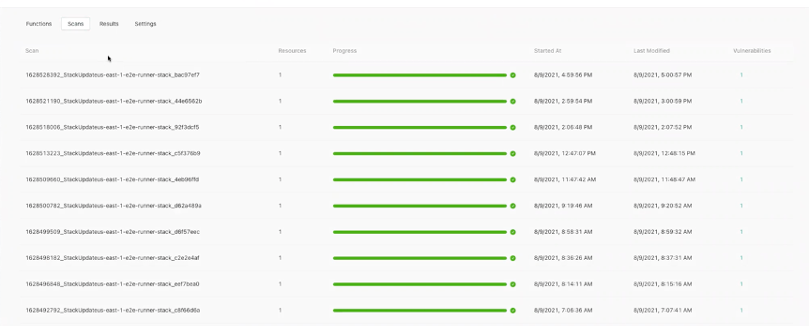
Contrast Serverless “Scans” provides a history of all application scans performed
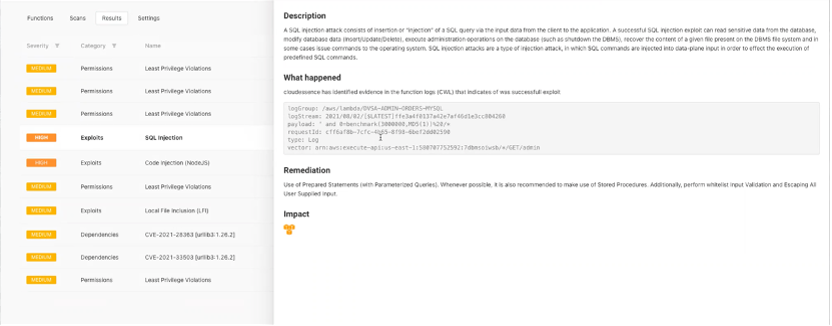
Results. The solution keeps a running list of scan alerts and assigns a “severity” rating (critical, high, medium, low) to each result (consistent with the risk ratings provided by the broader Contrast platform). Clicking on an individual alert result brings up details such as a description of the issue, a code-level view of what happened, and developer-friendly contextual remediation guidance for fixing the problem. This guidance may also include sample code to help expedite the repair process. Contrast also automatically tracks other AWS services and functions that will be impacted downstream.
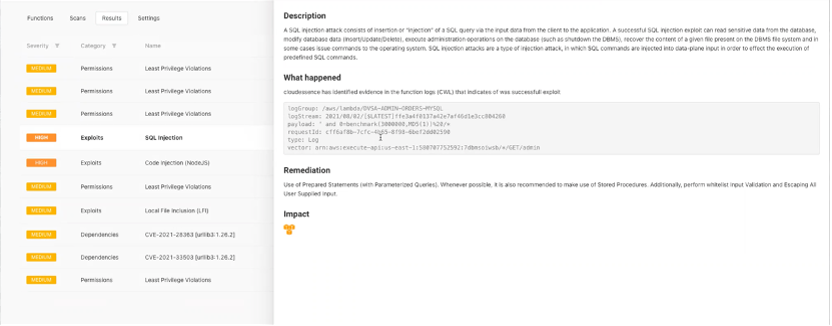
Contrast Serverless “Results” includes contextual remediation guidance
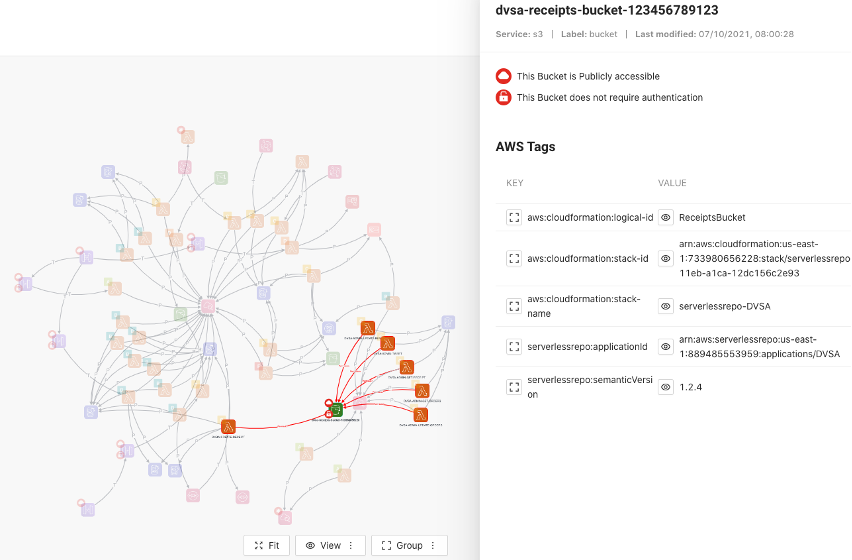
Graphs. Contrast also helps serverless developers visualize the relationship between functions and resources across the application. Clicking on a graph element (such as a specific Lambda function) shows both its connections and risk score. This helps users quickly understand the blast radius of a potential exploit and any associated elements that may also be affected. Users can customize their views according to the specific services that are most meaningful to the organization.
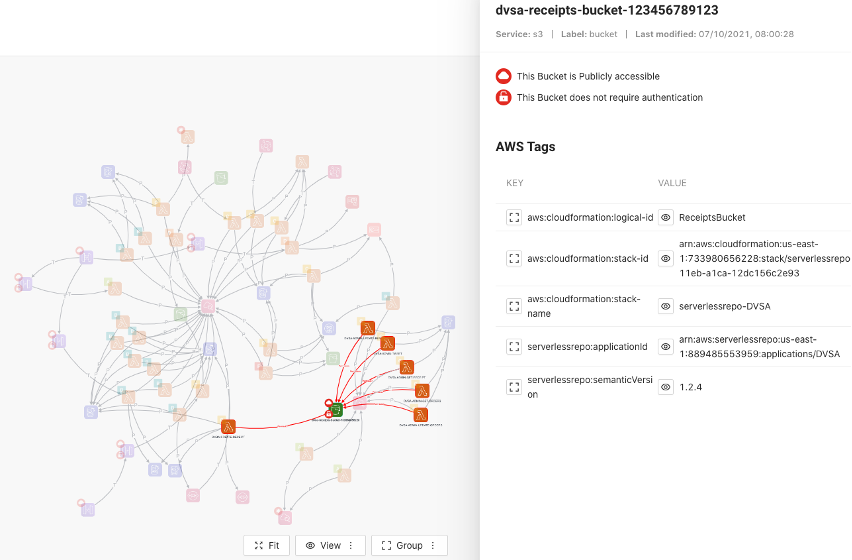
Contrast Serverless “Graphs” visualizes relationships between functions and services
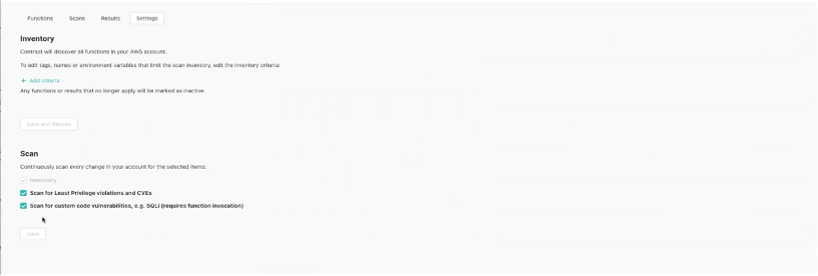
Settings. After the initial solution setup, users can always make additional changes to adjust their inventory and scan controls as needed. For example, a subset of the AWS account can be set up to work with Contrast Serverless Application Security. Application security teams can also configure which security scans run continuously for every change.
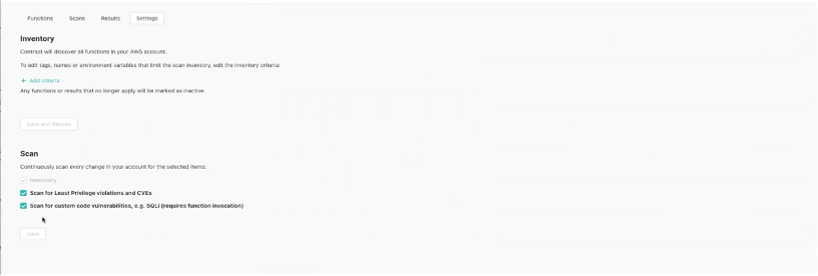
Contrast Serverless “Settings” allows for solution customization
Securing and Accelerating Serverless Development
While increasing the speed of developing new applications is a key benefit of serverless technologies, ignoring application security will only create new problems, costs, and delays downstream. It gets more expensive to fix vulnerabilities later in the SDLC while exposing users to a higher risk of application attacks.
Contrast Serverless Application Security allows developers to deliver higher-quality applications without the bottlenecks or inaccuracy of traditional AST solutions. And Contrast’s solution is purpose-built to do this within the native tools and workflows of serverless development platforms.
WHITE PAPER: Quickly and Easily Scale and Secure Your Serverless Applications With Contrast Serverless Application Security
REPORT: State of Serverless Application Security
PODCAST: Why Contrast Serverless Application Security Empowers Serverless Applications