By Jeff Williams, Co-Founder, Chief Technology Officer
April 25, 2014
We're Sorry You Got Hacked.
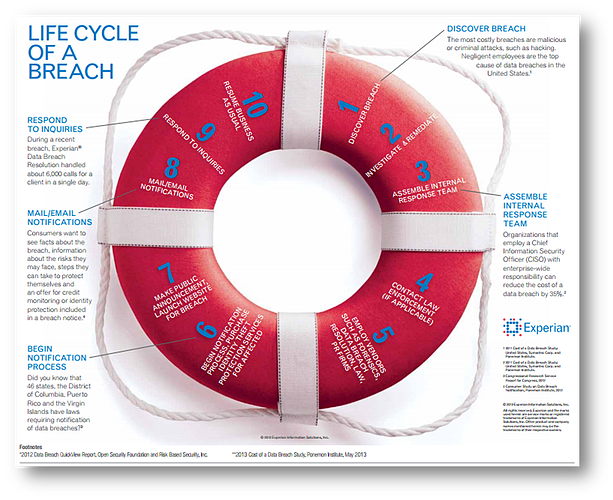
First, if you just detected a data breach, you've been hacked, and you should probably stop reading this blog post and get to work fixing the problem. If you need a "What to do in the first 24 hours after a data breach" refresher, check out Experian's tome here. It gives you good tips, lots of pertinent information, and is only partially biased (they, of course, want you to buy identify theft protection from them for those affected in the breach).
Second, consider yourself in good company. From TJ Maxx to Target to Nieman Marcus, some of the best and the brightest in every industry have experienced a data breach. In time, we're confident you'll rebuild your corporate brand and image. Like grandma used to say, time heals all wounds.
Third, if you are looking for a forensics team to discover where it happened, how it happened, etc. we'd recommend the top-notch firm KoreLogic Security. They'll help you discover the answers to the aforementioned questions in the most professional way possible. So whether you are dealing with script kiddies or an advanced groups of hackers, you'll be able to stop the data loss and resume normal activities in proper order.
And now that you've stopped the breach and rectified the situation as best you can, you can focus on the problem that likely put you in this mess: your web application security failed.
Somewhere in your stack of applications, you've got vulnerabilities. But you knew that already. That's why you've got firewalls, anti-virus, and malicious content protection systems -- to help you stay secure in spite of your vulnerabilities. But unfortunately, all your security technology doesn't really protect custom web applications and web services. And on average applications have 22.4 vulnerabilities *each*. That's why producing secure code and fixing your vulnerabilities are the ONLY way to protect your enterprise, and that's where we can help you succeed.
Get Developers Focused on Secure Code
Secure coding starts at the beginning with developers who know how to code securely. And since Universities world-wide struggle to stay relevant in teaching application security, rest assured, the problem is larger than you realize. Since knowledge varies by organization, you need to have an accurate baseline for what your staff currently knows and what they don't. The easiest way to do that is with Secure Coder Analytics from our friends at Aspect Security.
Secure Coder Analytics is a free quiz that tests your development teams knowledge about application security. Each 20-question quiz is randomized and covers basic topics required from organizations and compliance mandates like the OWASP Top Ten, WASC, and PCI DSS.
You sign up, send the email to your staff, allow them to take the quiz, and the aggregated results from your team's quizzes are sent to you in a chart format so you can see your team's strengths and knowledge gaps. Because when you know where your strengths and your "opportunities for growth" are, you can better align your educational training and learning management system to target areas that need the most work. If you know that you need to focus on eliminating cross-site scripting, then you are well on your way to more secure code.
Use Technology to Find and Fix Vulnerabilities During Development
Finding vulnerabilities earlier in the software development life cycle means you can fix them for a drastically reduced cost, saving you time, energy, and money. There are generally four ways to find vulnerabilities in applications, e.g. manual, dynamic, static, or interactive analysis, and each of them are useful in their own right. And when used together they can produce effective results.
As it turns out, the evidence you need to accurately identify and describe a vulnerability is usually scattered in a number of places. The big difference between the various tools is not whether they are static, dynamic, or interactive. What's important is what information the tools have available to identify vulnerabilities.
Why do we like the Contrast approach so much? Because we can use *ALL* this information, in real time, without any extra hardware or infrastructure, and without requiring a security expert to run the tool. There really is no comparison -- Contrast simply has too many advantages over existing approaches. It can help you find vulnerabilities before they become zero-day exploits. And at the end of the day, that's what everyone wants: to find and fix vulnerabilities. Get more information about Contrast via the demo link below.
.jpg)
Jeff brings more than 20 years of security leadership experience as co-founder and Chief Technology Officer of Contrast Security. He recently authored the DZone DevSecOps, IAST, and RASP refcards and speaks frequently at conferences including JavaOne (Java Rockstar), BlackHat, QCon, RSA, OWASP, Velocity, and PivotalOne. Jeff is also a founder and major contributor to OWASP, where he served as Global Chairman for 9 years, and created the OWASP Top 10, OWASP Enterprise Security API, OWASP Application Security Verification Standard, XSS Prevention Cheat Sheet, and many more popular open source projects. Jeff has a BA from Virginia, an MA from George Mason, and a JD from Georgetown.
Get the latest content from Contrast directly to your mailbox. By subscribing, you will stay up to date with all the latest and greatest from Contrast.