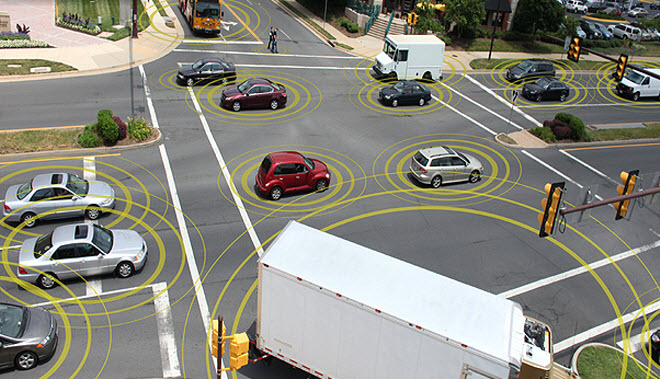
The fundamental problem is that the industry hasn’t created a thorough (and openly available) threat model that adequately considers what hackers might do. The analysis of V2V communications I’ve read focuses on safety issues — what happens under normal circumstances and even when crazy things happen on the road. There are numerous engineering challenges here, but the analysis doesn’t include malicious actors.
These safety considerations are nothing compared to the circumstances when a hacker gets involved. Consider the attacker jailbreaks a V2V communication system. Now he can send arbitrary messages to any other vehicle at any time, tricking the device into issuing alerts to drivers.
What if the attacker can send a message that contains an exploit for the system in your car? This provides the attacker the ability to do anything that is within the physical capability of the V2V system. Even start to attack other reachable systems within the car. To my knowledge, current V2V isn’t intended to allow access to brakes, steering, etc… However, manufacturers are motivated to consolidate computer systems. Why deploy two when one will do? The history of security isn’t good in these situations. Attackers have been incredibly adept at bridging from one system to another.
On balance, though, I think V2V will be good for overall safety. There will certainly be vulnerabilities, which we will fix. And there may be attacks, which may be disastrous. But I believe this will be a huge net positive for driver safety. I just wish we didn’t have to always field technologies with massive security holes and then spend decades patching them up. Relying on unpaid security researchers seeking BlackHat fame just doesn’t seem like the right model when people’s lives are on the line.