Traditional Scanning Tools Can’t Keep Up
The legacy application vulnerability scanning tools in place at most organizations today were built for an entirely different era of applications and development. Their functionality predates today’s complex, distributed software that is comprised of open-source libraries, third-party components, and application programming interfaces (APIs). Nor were they designed for the fast-paced demands of modern Agile and DevOps environments.
Used within a typical development pipeline, traditional static application security testing (SAST) tools have a number of critical issues that force many organizations to choose either speed or security. As a result, more than half of developers admit to skipping security scans in order to meet deadlines. These problems include:
The vast majority (91%) of organizations say that vulnerability scans take at least three hours—and for 35%, they take eight or more hours. Once a scan report is finally generated, it takes the average security team an hour per alert for triage and diagnosis. And once an alert is confirmed as a true vulnerability, developers typically spend at least four hours locating the root cause of the vulnerability and fixing it. In addition, developers spend another six hours per week verifying that their remediation efforts actually fixed the issues and that they didn’t introduce new problems in the code.
The poor accuracy seen with traditional scanning tools comes from the fact that they attempt to build a model of the application in order to project its behavior at runtime (and subsequently its vulnerabilities). As much as 85% of the alerts in each scan are false positives—and noisy results quickly lead to alert fatigue among staff. These traditional scan results also inhibit an organization’s ability to correlate, prioritize, and remediate potential application risks. As a result, developers often waste time on things that pose no risk at all. Critical vulnerabilities may not get fixed in a timely manner—or they may be missed entirely and make their way into production.
Most of the old static analysis testing solutions don’t offer friendly guidance geared to help developers quickly find and fix vulnerabilities without involving security experts. This directly contributes to a growing backlog of unremediated vulnerabilities; it takes the average organization 121 days to fix only 50% of issues. Businesses with higher security debt tend to fall even further behind with progressively higher volumes of vulnerabilities—1.7x higher than for organizations with below-average security debt. And because these tools predate modern environments, they also usually don’t integrate with today’s DevOps-native tooling such as ticketing systems, chat tools, and continuous integration/continuous deployment (CI/CD) pipeline systems.
Organizations require a pipeline-native approach to scanning that integrates into DevOps/Agile workflows, tooling, and systems. This kind of static analysis testing harmonizes the objectives of development and security teams to enable both faster development cycles and higher quality code. A pipeline-native SAST approach provides focused results and actionable context while empowering organizations to accelerate delivery schedules without application security causing delays.
Organizations need to prioritize the vulnerabilities that matter most. This enables them to efficiently manage their limited application security staff resources. To support this objective, pipeline-native scanning provides highly accurate results that focus on critical vulnerabilities that can lead to exploitation. This provides high confidence in risk-prioritized findings that focus on remediation. It also supports a single set of harmonized results across all facets of application security and across the software development life cycle (SDLC), including application security testing (AST), software composition analysis (SCA), and runtime application protection and observability.
Scanning cannot be retrofitted into the modern development pipeline. The underlying scanning technology must be built from the ground up to adapt to modern pipeline configurations, have an experience that is familiar to those using and supporting the development pipeline, and not “break the process.”
To help eliminate the security analyst bottleneck, pipeline-native scanning should also provide developer-friendly “how-to-fix” guidance. Accurate results that include contextual information enable development teams to quickly find and fix vulnerabilities without waiting on security experts. This not only accelerates remediation times, but it also educates developers and helps them avoid similar issues in the future.
Pipeline-native scanning also provides a step function improvement in scan time. Focusing only on exploitable flows in the application runtime is not only faster, it also improves overall security performance. It allows organizations to fix issues earlier in the development pipeline, which reduces remediation costs—fixing a vulnerability gets more expensive the further from where the error was introduced in the development process.
Contrast Scan delivers a revolutionary pipeline-native approach to scanning—delivering the fastest, most accurate static analysis scanner available today. As the latest addition to the Contrast Application Security Platform, Contrast Scan helps organizations streamline DevOps workflows, accelerate vulnerability remediation, and deliver secure code on schedule.
Deploying Contrast Scan is quick and easy; it requires zero configuration and literally three clicks to start scanning right out of the box. It offers native-built plug-ins with Maven, GitHub Actions, and Gradle for continuous integration/continuous deployment (CI/CD) pipeline automation as well as a command line interface (CLI) and extensible application programming interfaces (APIs) for SDLC integrations.
Contrast Scan is fast—10 times faster than traditional tools. It focuses only on vulnerabilities that are actually exploitable, eliminating non-issue noise and helping teams focus on high-priority problems. Faster scan times help remove the bottlenecks that slow delivery schedules, improve the efficiencies of security and development teams, and reduce operating expenses (OpEx).
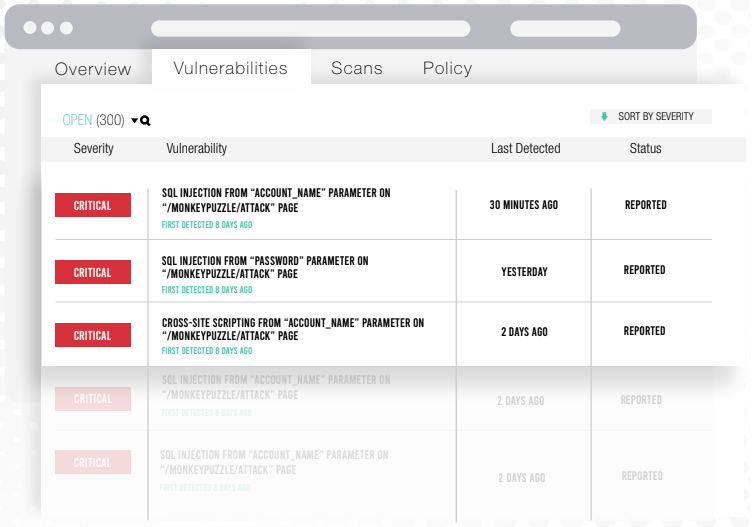
Figure 1: Contrast Scan prioritizes critical vulnerabilities.
Contrast Scan’s demand-driven algorithm was built from the ground up to work in the development pipeline (and not retrofitted with webhooks or integrations). In addition, Scan also offers an experience that is familiar to developers using the pipeline and DevOps teams supporting them. Scan comes with purpose-built CI/CD plug-ins. We started with build automation plug-ins for Maven and Gradle to focus on the point of maximum impact, where the fully compiled binary is first available. Scan is also adaptable to any modern pipeline configuration through an extensible API.

Figure 2: Pipeline-native scanning that integrates with existing toolsets.
As a key solution in the Contrast platform, Contrast Scan helps accelerate remediation times up to 45x. It achieves this by enabling developers to focus on exploitable flows, prioritize routes with entry points based on runtime and production traffic analysis, and leverage actionable “how-to-fix” guidance. Organizations can reduce their security debt while eliminating application security risks. The Contrast platform complements this by providing runtime protection for any open or unknown vulnerabilities in production.
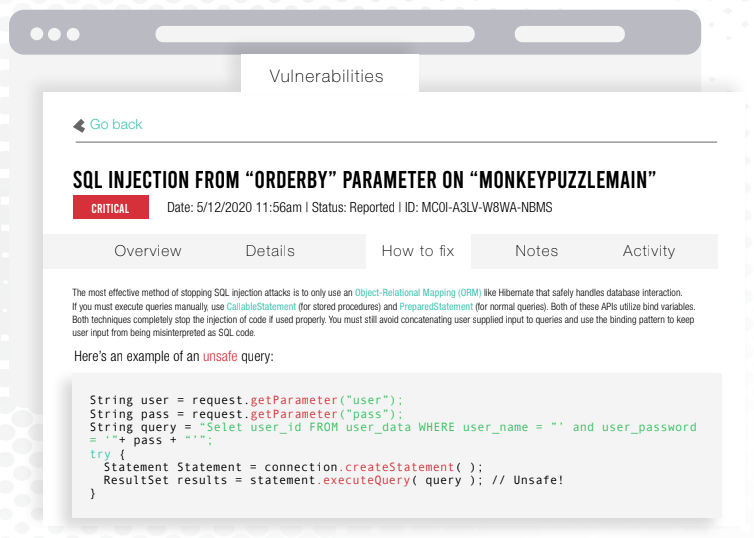
Figure 3: Contrast provides context-rich remediation guidance for developers.
Pipeline-native static analysis testing can help security teams improve their scan, triage, and remediation efficiencies by nearly a third (up to 30%). The Contrast platform allows organizations to incorporate security as a seamless aspect of their rapid DevOps release cycles. Integration with existing CI/CD tooling from build to production ensures seamless workflows, tracking, and communications. Contrast’s approach also helps streamline compliance reporting—greatly reducing the time needed for auditing and reporting processes.
As the latest addition to the Contrast Application Security Platform (along with Contrast Assess, Contrast OSS, and Contrast Protect), Contrast Scan extends a true DevSecOps approach to application development. It essentially makes shipping code with zero critical vulnerabilities a reality for application developers. All combined, the platform now provides harmonized analysis, testing, and exploit prevention capabilities across the SDLC and in each critical phase of the CI/CD pipeline:
The Contrast platform was purpose-built for securing modern applications, assisting the people who develop them, and streamlining the systems used to build them. Contrast Scan is just the most recent example of how we’re baking security into that ecosystem.
Make sure to reserve your spot for our webinar featuring some all-star guest panelists on June 10. I also included the Inside AppSec Podcast featuring an overview of the reason we built and launched Contrast Scan.
Webinar: Contrast Launches the SAST of the Future—Pipeline-native Static Analysis
Inside AppSec Podcast: Contrast DevSecOps Platform Now Includes Pipeline-native Static Analysis
Get the latest content from Contrast directly to your mailbox. By subscribing, you will stay up to date with all the latest and greatest from Contrast.