By David Lindner, Chief Information Security Officer
August 4, 2021
Application Security Observability Report Finds Median Time To Remediate Is 3 Days Versus 86 Days
Security debt—the backlog of known and unresolved vulnerabilities in an organization’s applications—is a real burden on organizations when it gets too high. As our own Jeff Williams wrote recently in Forbes, “It is like a weight that DevOps and security teams carry around, limiting what other burdens they can carry at the same time.” He continues:
When an organization has a large security debt, it must prioritize which vulnerabilities are most urgent to fix. But since most teams lack an automated way to do this, they find themselves spending significant time doing risk rating and managing the backlog. This leaves them with little time to actually remediate the vulnerabilities—which is the whole point of finding them. Vulnerabilities start to pile up—just like clothing in the closet or junk in the garage.
The first step in reducing an organization’s security debt is to get to the point where new vulnerabilities are resolved in a timely manner—rather than adding further to the backlog. Fortunately, Contrast Labs’ new 2021 Application Security Observability Report finds that Contrast customers deliver both improvements in time to remediation and reductions in security debt per application.
The Application Security Observability Report analyzes a year’s worth of telemetry from thousands of real-world applications and application programming interfaces (APIs) onboarded on the Contrast Application Security Platform. Our customers come from every major industry in a variety of geographies, and their applications range from customer-facing to back-office solutions. We were able to compare our customers’ results with published findings from a traditional static application security testing (SAST) vendor.
One thing we discovered was that our customers successfully remediate more custom code vulnerabilities than users of traditional SAST tools. The fix rate for serious vulnerabilities was 97% for Contrast customers—18% better than the 82% reported by the traditional SAST vendor. This difference can potentially represent hundreds of serious vulnerabilities that are never addressed.
The superiority of the Contrast platform is even more evident when looking at how long it takes the typical organization to resolve half of its custom code vulnerabilities—the median time to remediate. Among vulnerabilities that are ultimately fixed, the traditional SAST vendor reports that its customers take 86 days on average to reach this milestone—28.7 times the 3 days reported for the Contrast customer base. Among all vulnerabilities, the figures are 11 days versus 216. Needless to say, this is an impressive achievement for users of the Contrast Application Security Platform.
Traditional SAST scans are time-consuming, and the reports require triaging and analysis by the security team before they can be handed back to developers for remediation. For a clear majority of organizations, recent research by Contrast found that for a majority of organizations, SAST scans take at least five hours. This means that it can be days or weeks after a vulnerability is created before developers have a chance to fix it with traditional approaches.
Contrast, on the other hand, does continuous scanning from within the application and provides immediate, detailed feedback as soon as a vulnerability is created. This enables a developer to fix the problem before many layers of new code are added to complicate things. It also keeps time-to-remediate metrics very low.
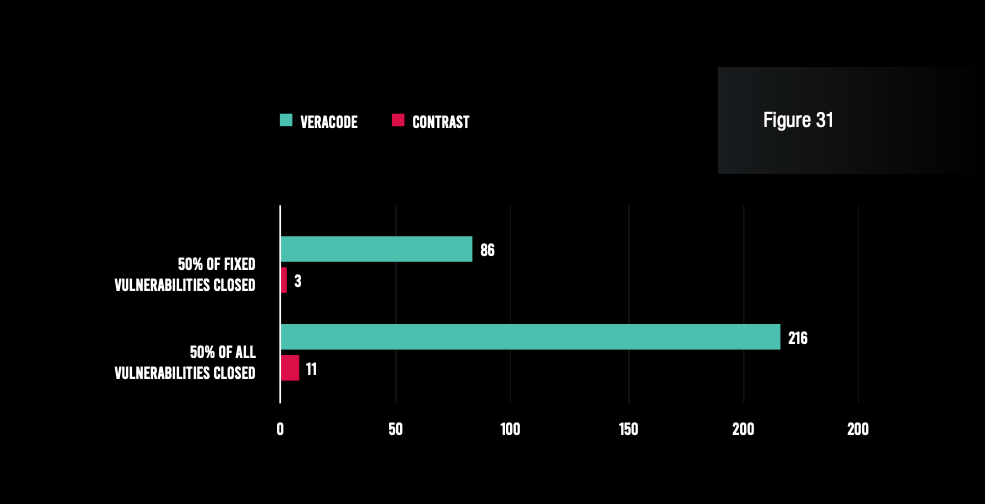
Contrast customers achieved a median time to remediate for fixed vulnerabilities of just 3 days, compared with 86 days for traditional SAST.
This faster remediation has had a positive impact on the security debt held by the typical application. Our 2020 Observability Report found an average of 26 backlogged vulnerabilities per application for the prior 12 months, and that number has declined to 21 this year—a 19% improvement.
This is despite the fact that many of our customers added highly complex applications to the dataset since last year, and that many new customers have been added that have less tenure with the solution. These factors together account for a 190% increase in the number of applications being monitored. Thus, the fact that the average backlog per application declined at all for the overall dataset means that significant improvements were made with the applications that have been on the platform longer.
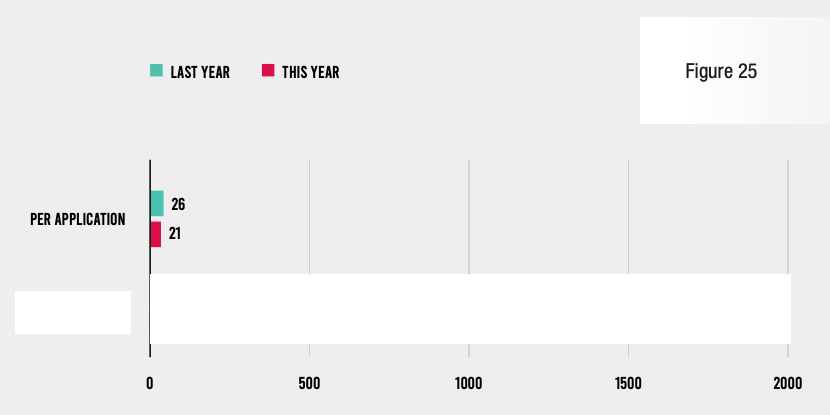
Security debt per application declined by 19% for Contrast customers, compared with a year ago.
The above discussion addresses two separate topics: time to remediate and security debt. Most readers would agree that the two concepts are connected, but their interrelatedness only became clear when we cross-analyzed these two metrics in our dataset.
Specifically, when we isolated the organizations with below-average security debt, we found that their median time to remediate all vulnerabilities was just 2 days rather than 11 days—a 550% improvement. Just as impressive, such organizations reach the milestone of 75% remediation in just 74 days, as opposed to 249 days for the entire dataset (versus 540 days for traditional SAST). Clearly, having less security debt to worry about allows organizations to focus more fully on resolving current vulnerabilities in a timely manner.
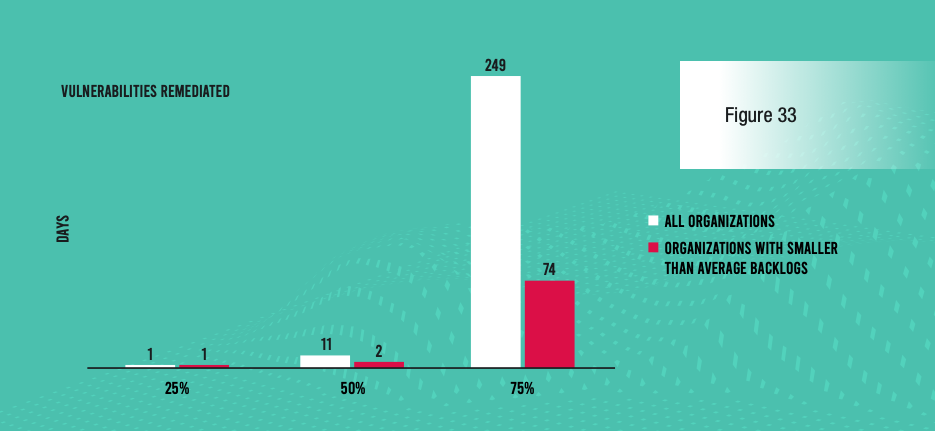
Organizations with smaller than average security debt improve their median time to remediate by 550% over the overall customer base.
The 2021 Application Security Observability Report makes it very clear that users of the Contrast Application Security Platform enjoy distinct advantages over those taking traditional approaches. Following are three key takeaways from the report’s remediation time and security debt findings:
These findings are just a small part of what is brought to light in Contrast’s flagship annual report on application security trends and practices. Be sure to download and read the entire report! Here are some other highlights from its findings:
REPORT: 2021 Application Security Observability Report
PODCAST: Key Insights on Security Debt and the Vulnerability Escape Rate Trends (New Report)
WEBINAR (Register): Key Insights and Benchmarks From Contrast’s 2021 Application Security Observability Report
VIDEO: Introducing Contrast’s 2021 Application Observability Report

David is an experienced application security professional with over 20 years in cybersecurity. In addition to serving as the chief information security officer, David leads the Contrast Labs team that is focused on analyzing threat intelligence to help enterprise clients develop more proactive approaches to their application security programs. Throughout his career, David has worked within multiple disciplines in the security field—from application development, to network architecture design and support, to IT security and consulting, to security training, to application security. Over the past decade, David has specialized in all things related to mobile applications and securing them. He has worked with many clients across industry sectors, including financial, government, automobile, healthcare, and retail. David is an active participant in numerous bug bounty programs.
Get the latest content from Contrast directly to your mailbox. By subscribing, you will stay up to date with all the latest and greatest from Contrast.