Contrast Labs' analysis of real world application security data from March 2018. We're going to change it up a bit this month by expanding our coverage to include:
- Both known and unknown vulnerabilities in custom code
- Both known and unknown vulnerabilities in libraries and frameworks
- Attacks on applications and APIs
To learn more about how Contrast directly measures both vulnerabilities and attacks in parallel across your application portfolio, please visit our website.
Overview
- In March, we observed another large increase in attack volume, primarily from the United States. Following the trend from February, every single application in the analysis was attacked at least once during the period.
- The most common serious vulnerabilities are Clickjacking, XSS, Path Traversal, Weak Crypto, and SQL Injection, but these vary significantly by language.
- This month saw continued dominance of injection attacks of all types (XSS, SQL, CMD, PATH) and added a significant rise in CSRF and Padding Oracle attacks. Attacks on CVEs, particularly Struts, also continued in March.
- March brought significantly longer attacks than February, averaging 24.9 minutes. The longest attack more than doubled to 28.3 hours.
Observations: Vulnerabilities
- General
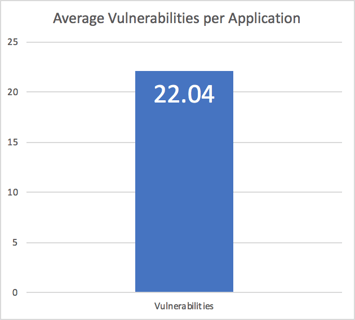
- Overall, vulnerability rates are very high. On average, we report 22.04 serious vulnerabilities per application. That rate of serious problems would not be tolerated in other industries.
- Custom Code
- In every language, Clickjacking, XSS, SQL injection, and Log Injection vulnerabilities are near the top of the list. However, XSS was the only vulnerability to make the top six in .NET, Java, and Node.js.
Table 1 - Top Custom Code Vulnerabilities by Language
| .NET |
Java |
Node.js |
| log-injection |
reflected-xss |
unvalidated-redirect |
| event-validation-disabled |
log-injection |
hardcoded-key |
| compilation-debug |
sql-injection |
hardcoded-password |
| request-validation-disabled |
redos |
reflected-xss |
| max-request-length |
trust-boundary-violation |
cache-controls-missing |
| reflected-xss |
crypto-bad-mac |
clickjacking-control-missing |
- Libraries and Frameworks
- Java averages 3.4 vulnerable libraries per app. .NET is much better, averaging only 0.5 per application. Node.js has 1.8 and Ruby has 0.7 vulnerable libraries per application.
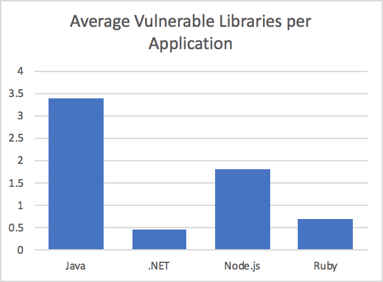
- Note that Java apps average 64 libraries per application while .NET apps average only 12. Meanwhile, both Node and Ruby applications average over 130 libraries per application.
- Java's libraries are also the least used - with only 8% of libraries actually executed. Applications in other languages execute over 30% of their library code.
Observations: Attacks
- Custom Code
- Almost 60% of applications were targeted with Path Traversal in March. SQL Injection, XSS, and Command Injection are also very likely attacks. Every application was attacked using at least one vector.
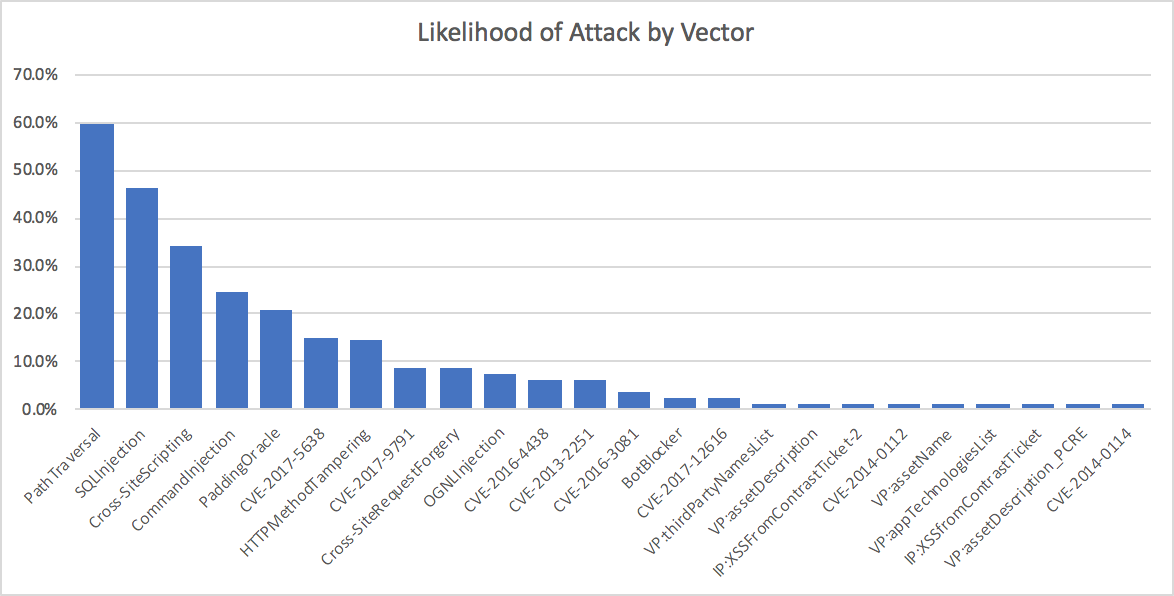
- More than 20% of applications were hit with Padding Oracle attacks in March, up dramatically from January. Be careful with your error messages!
- CVEs
- Attacks on CVEs were experienced by nearly every application in March. CVE-2017-5638 (Struts2) attacks are still quite prevalent after a year since being disclosed and the massive attention received.
- Probing for all Struts2 vulnerabilities remains pervasive. Be sure you have updated your libraries or implemented Runtime Application Self Protection (RASP).
- Geolocation
- March saw application layer attacks from 5 continents, 31 countries, and thousands of cities around the world. While attacks came from all over the world, the overwhelming majority originated in the United States. In the map below, the number of attacks is shown as dark green (most), light green, yellow, orange, and red (least).
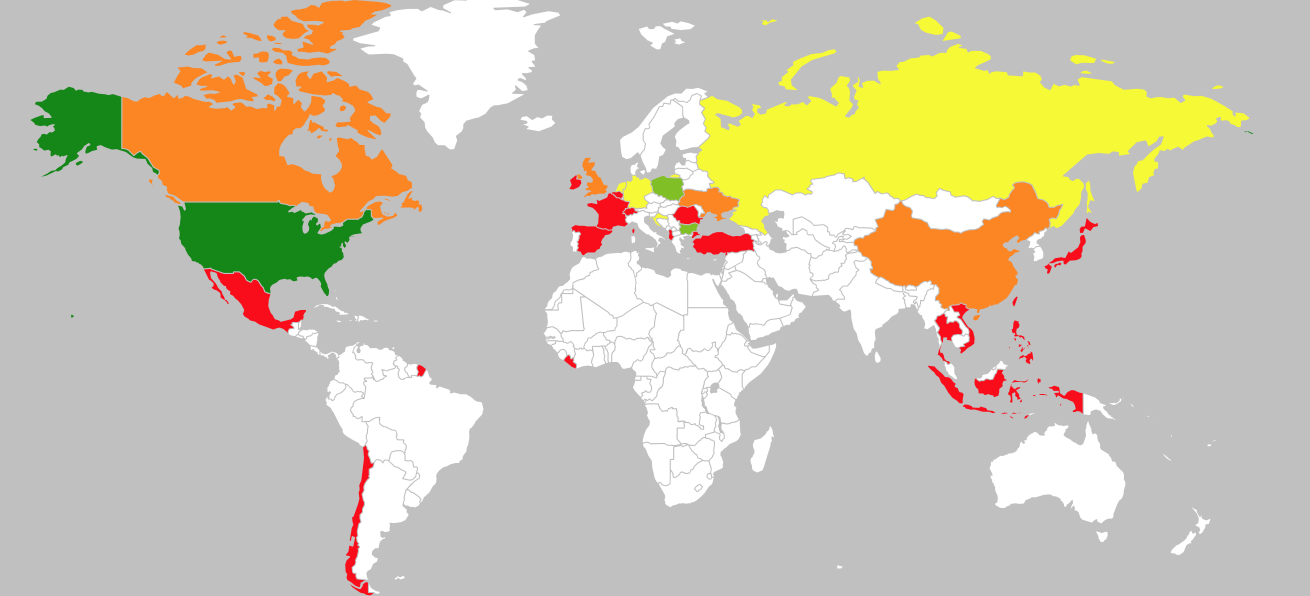
- Chesterfield, Missouri is still our attack leader, with five months in the number one spot. Hartford, Connecticut remains in second place.
