The Runtime Security Company
Learn about the hidden dangers of traditional application security (AppSec) tools and why the Runtime Security platform is replacing them

2023 Gartner Peer Insights Voice of the Customer for AppSec Testing
Contrast Security was recognized with an overall customer rating of 4.7 out of 5.0 out of 37 reviews as of August 2023 and a 94% willingness to recommend the product. Read the full report to learn more!
Replace Broken AppSec Tools With Security Processes That Actually Work: Runtime Security
Runtime Security uses sophisticated instrumentation to reshape existing security processes so they’re more proactive and insightful.
Empowering application developers to see and fix application security risks in real-time
See how Contrast customers are accelerating development release cycles by shifting smart in the software development lifecycle to give application developers greater power to protect their own code.
The Contrast Secure Code
Platform
Ignite innovation velocity on the only unified security platform built to get secure code moving through the entire application development pipeline and continuously protect your apps across the complete software lifecycle.
The Contrast Unified Platform Approach
Dev
Test
Prod
Empower developers to
secure as they code.
Ensure high-assurance
software delivery.
Know your attackers.
Stop exploits cold.
Contrast
Scan
The fastest and most accurate Static Application Security Testing (SAST) tool ever built
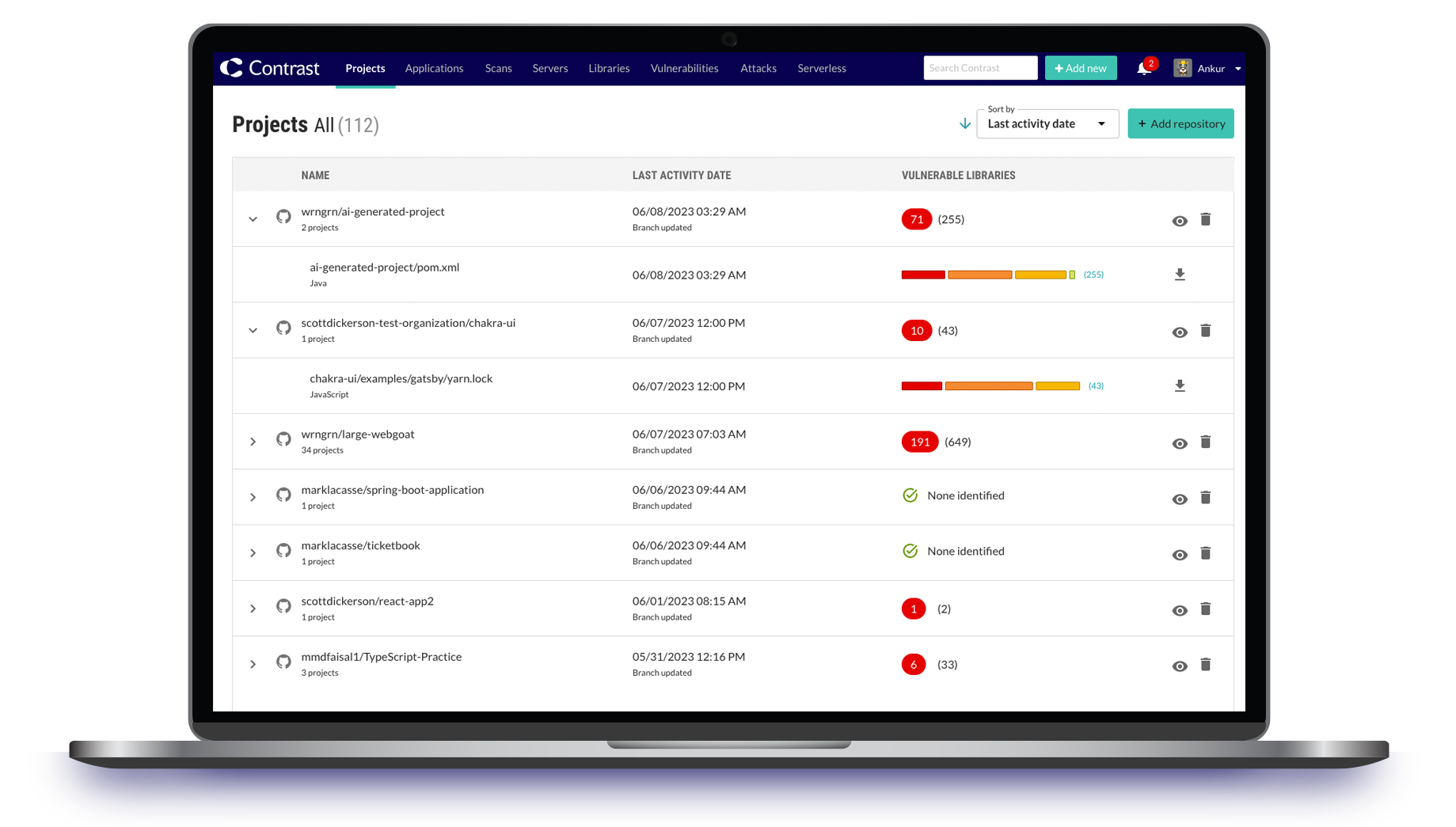
Contrast
SCA
Find vulnerabilities in your third-party dependencies and know which are used at runtime (typically 1/3)
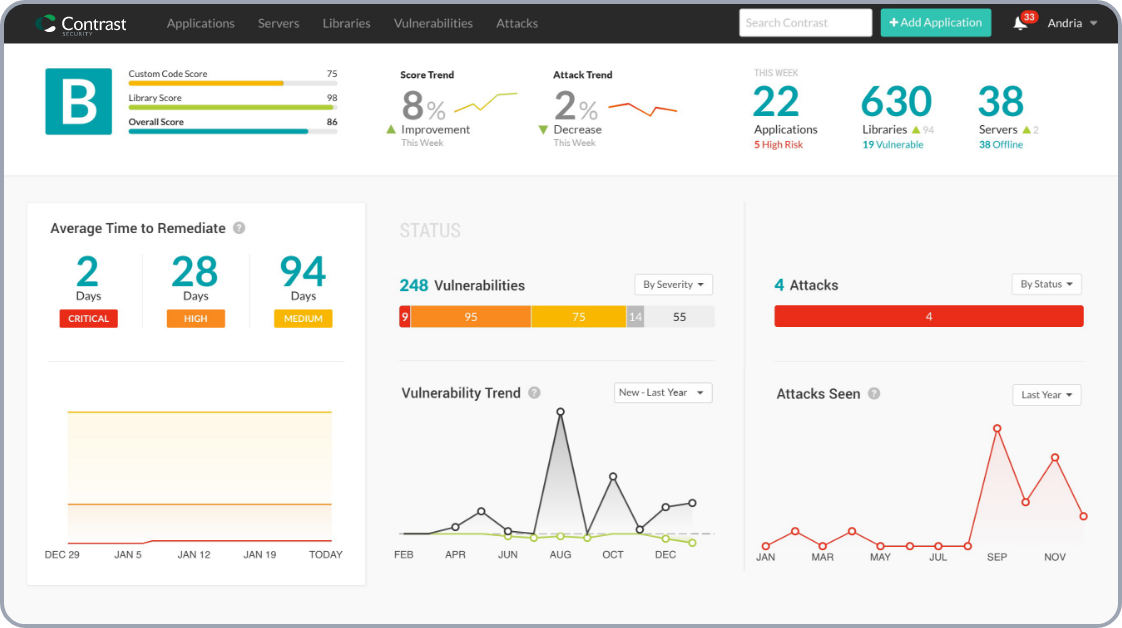
Contrast Security Delivering Real World Results for Application Security Improvement
%
INCREASE DEVELOPER PRODUCTIVITY TIMES
Let developers develop, freeing up 5 hours a week per developer.
%
THREE-YEAR
ROI
Lower total cost of ownership. Payback in five months.
%
REDUCTION IN VULNERABLE APPS
Harden application security across the enterprise.
Built for Developers. Trusted by Security.



Experience Contrast Today
Schedule a one-to-one demo to see what the Contrast Secure Code Platform can do for you.
Secure as you code
See and eliminate application security risks in real-time with security integrated seamlessly into your application development workflows making it easy for you to ensure compliance and meet release deadlines.
Protect your business without slowing it down
Make application security seamless & scale your ability to protect by empowering every developer to build secure code from the start whilst gaining unique visibility & control to manage risk at every step from development to production.
From Repo to Runtime — Full Spectrum Software Composition Analysis Across the SDLC
Contrast Security now provides repository level SCA integrated into its platform through the Contrast GitHub App. It provides visibility into known vulnerabilities from dependencies in code repositories with results shown in GitHub pull requests and in the Contrast UI. It provides visibility with simple onboarding, allowing for integration at scale.
Customer Spotlight: Snap Finance
Kiran Sharma, Senior Privacy Program Manager at Snap Finance, highlights the significant impact of Contrast’s platform on their security initiatives. The Contrast Secure Code Platform emerged as the ideal solution, providing Snap Finance with comprehensive insights and actionable information to tackle vulnerabilities effectively.

Increase Application Value
and Resilience
Advanced application security that frees developer time to accelerate the value your applications deliver whilst leaving you confident that the software your business is built on is continuously protected against advancing threats.
Gartner® visionary
6 Consecutive Years in Magic Quadrant™
17X Faster Remediation
AST vs. a Legacy SAST Vendor
Scored 4.8 out of 5.0 stars
3 Consecutive Years in Gartner Peer Insights
96% customer recommend
AST vs. a legacy SAST Vendor
Watch On-Demand
ContrastLive
Cybersecurity experts showcase the latest product releases and newest features within the Contrast Platform, discuss latest industry news and hot topics, and answer questions from the audience.
Customers Get Secure Code Moving with Contrast
We use Contrast to actively integrate security into the SDLC. Contrast allows developers to see in real-time, the impact of their coding decisions so that they can make changes.”

4.7
Contrast speeds up the delivery pipeline – we fix issues earlier in the development lifecycle. Great for any company trying to achieve a DevSecOps approach to application security.”

4.7
With Contrast, we have automated and streamlined our application security testing without having it slow us down in our continuous development environment.”

4.7
Code Patrol Podcast
Code Patrol discusses all things security — be it cybercrime, hacking, DevSecOps and beyond — that collide with the code that runs the world.
Resources

AppSec Observer
Blog
Learn about real-world insight and “in-the-trenches” experiences on topics ranging from application and information security to DevOps and risk management.

Contrast Incident Response Hub
Incident Response
The latest news, solutions and best practices for vulnerability management and incident response.

News Room
Media Coverage
Check out Contrast's latest media coverage and explore the archives.
Contrast is a strong performer
Contrast is recognized in the 2023 Gartner® Peer Insights™ Voice of the Customer for AppSec Testing with an overall customer rating of 4.7 out of 5.0 out of 37 reviews as of August 2023, and a 94% willingness to recommend the product.

Shift Smart with Contrast Security
See how you could get secure code moving on the Contrast Secure Code Platform