Come flu season, you have two options – cover your face with a mask and hope you don’t catch anything. Or, do the responsible thing: get a flu shot and protect your entire body and immune system from within. For your software applications, it’s always flu season. Read on to see how a WAF (Web Application Firewall) compares to Contrast Protect, our Runtime Application Self-Protection (RASP) solution.
Come flu season, you have two options – cover your face with a mask and hope you don’t catch anything. Or, do the responsible thing: get a flu shot and protect your entire body and immune system from within. For your software applications, it’s always flu season. Read on to see how a WAF (Web Application Firewall) compares to Contrast Protect, our Runtime Application Self-Protection (RASP) solution.
Web Application Firewalls (WAF) – The Mask
Trying to protect critical web applications is a similar decision. You may keep using your WAF – the proverbial corporate winter mask for your applications – and hope you’re protected and not disrupting customer experience. But there are some known WAF drawbacks:
- Limited Visibility & Protection: The mask covers your face – what about the rest of your body? WAFs sit outside the application and only examine network traffic
- Poor Accuracy: It may block some germs, but not all of them. At the same time, it may keep out the good stuff too. Since WAFs are signature based, they fundamentally lend themselves to false positives – i.e., blocking the good stuff
- Slow to deploy: Is the mask fully covering your mouth? Nose? What about your hands, they spread germs too? WAFs require co-ordination with multiple teams and considerable tuning to stand up
- Hard to scale: You need to remember to take your mask wherever you go. In addition, you will need to buy more than one.
Contrast Protect - The Flu Shot
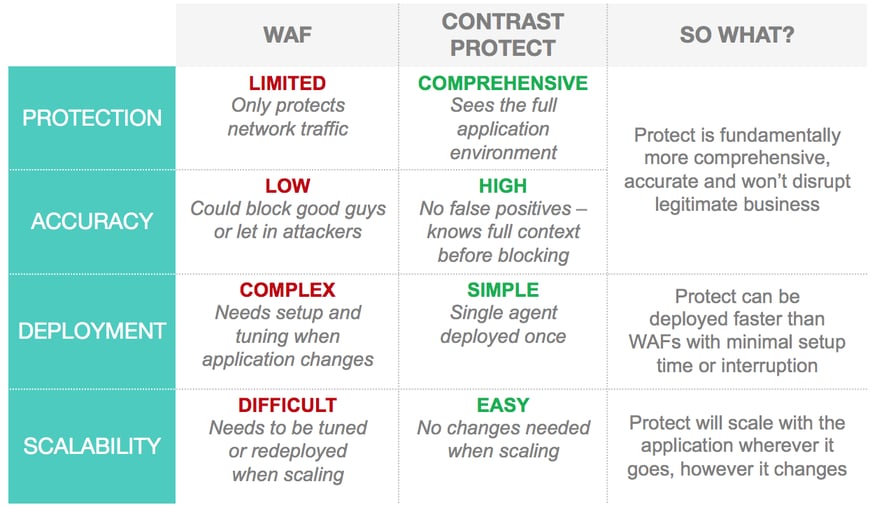
Consider Contrast Protect – A one-time, highly targeted flu shot for your applications. You deploy once and it protects your applications from within. It has visibility into the full application stack, goes where your applications goes, and as your applications change, it immediately adjusts. The following table outlines how Contrast Protect improves your overall software application security posture and protects your applications in real-time within minutes. We also highlight some of the WAF drawbacks.
Table 1: How Contrast Protect compares to a WAF.
Contrast Protect Sees More and Blocks Better
Adding Contrast Protect to your security stack instantly gives you real-time protection, lower false positives and a “set it and forget it” approach to deploying and scaling application security.
Deeper Visibility, Real-time Protection
Contrast Protect’s patented deep security instrumentation allows it to go deeper into the stack. This allows you to (1) protect the full application stack, (2) gather detailed information about an attack as it happens and (3) block the attack instantly. For each attack, Contrast sees:
- Full HTTP request
- Stack trace (including lines of code)
- Targeted web page/folder
- Targeted server
- Attack vector details
- Attacker IP address
- Application account associated with attack
- Attack specific data (not exhaustive):
- XSS: HTTP response data
- SQLi: Full database query
- Path Traversal: Full file path
- Padding Oracle: Exception details
- Command Injection: OS command
- Remediation guidance
- Time of event
- Rate of attack
- Severity of attack
Fundamentally More Accurate Approach
Most WAFs use signatures or regular expressions as the decision engines to detect and block attacks. Contrast Protect analyzes how the application treats the network traffic to understand true impact. Therefore, Protect’s decision to alert or block is based on facts gathered at real time. WAF decisions are, on the other hand, predictions.
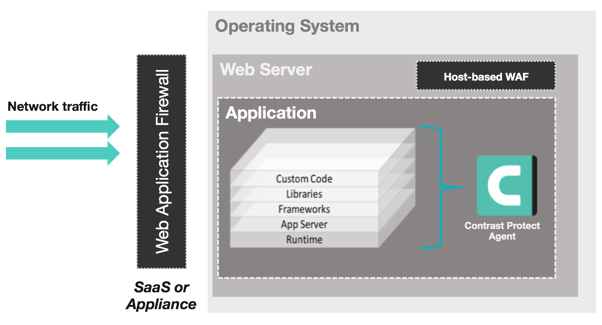
Figure 1: Standard Web Application Firewall compared to Contrast Protect Agent Architecture.