Software is at the heart of Digital Transformation, and organizations are using software more than ever for economic and productivity purposes in order to transform the way they run their business – to address customer needs, for better customer experience, greater efficiency, faster time to market and cost optimization. In short, organizations need to stay relevant, competitive and well positioned by delivering solutions and reacting to business and technology changes. OSS is turbo charging these efforts by enabling organizations to reuse the software assembled via the open source community in order to deliver to market even faster.

Figure 1: Digital Transformation of Business via Software
The Ubiquity of Open Source Software
The adoption of third-party OSS has increased significantly over the last few years to help augment proprietary code developed in-house and to accelerate time-to-market. This use of OSS speeds application development and helps gets compelling business applications to market faster.
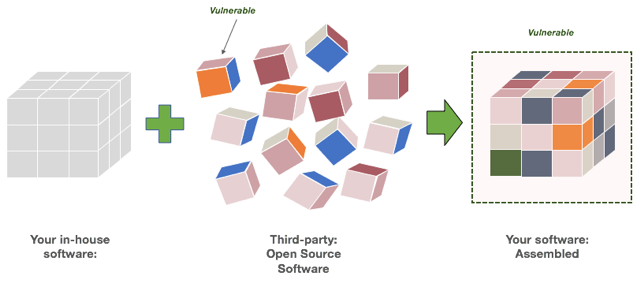
Figure 2: In-house and external Open Source Software
Open Source Introduces Vulnerability and Risk to the Equation
Adopting OSS reduces overall development costs and frees developers to work on more value-added tasks. However, as companies use open source code, they risk introducing vulnerabilities that predispose them to getting breached.1
A quick look at the stats reveal the risks...
- 96% of applications include some form of OSS
- 67% of applications contain open source vulnerabilities
- 90% of software applications are NOT security tested
- 41% of vulnerabilities are detected and remediated manually
Libraries & Custom Code
Given the risks, it is critical that organizations understand the composition of their software applications. For example, the majority of application source code (79%)2 is comprised of libraries. Obviously, these libraries must be actively managed and organizations should continuously monitor for known vulnerabilities in actively used libraries because of the potential risks they represent.
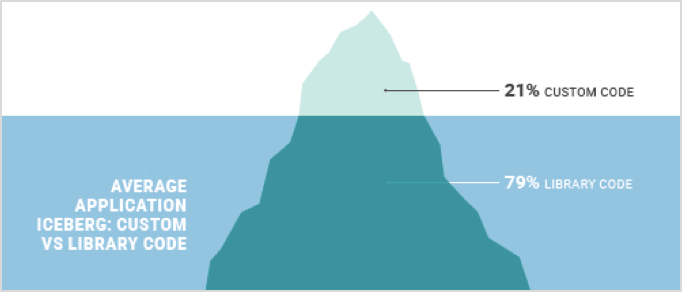
Figure 3: Contrast Security: State of Application Security 2017
Increased Software Risk Means More Business Risk
Applications that use OSS are a primary target for cybercriminals because once vulnerabilities in OSS are discovered, adversaries can attack virtually any application built using that now-vulnerable OSS. That means software development, security and operations teams must factor in and address the risk of OSS. And, with more of every business based on software, those software risks are in fact business risks.
Security – The Key Component of Digital Transformation and Software Development
Digital transformation is driving the creation of more software, delivered faster. OSS helps meet the need for speed, but can introduce unanticipated risk to the business. Contrast Security is uniquely positioned to deliver affordable, automated application security solutions that address OSS risk at scale. We enable development and security teams to embed application security within the entire Software Development Life Cycle (SDLC) quickly and inexpensively from development, QA and production. Our products make software “self-protecting”, so applications built on OSS can be created and deployed into production faster across many environments without compromising on their security.
As Jeff Williams, CTO, Co-founder, Contrast Security states:
“It used to be that attacks would take weeks or months to emerge after an application vulnerability was disclosed. Today, that safe window has been reduced to about a day, and will probably be only a few hours in 2018.”

References:
1) Open Source Security Analysis, 2016
2) Contrast Security: The State of Application Security, 2017