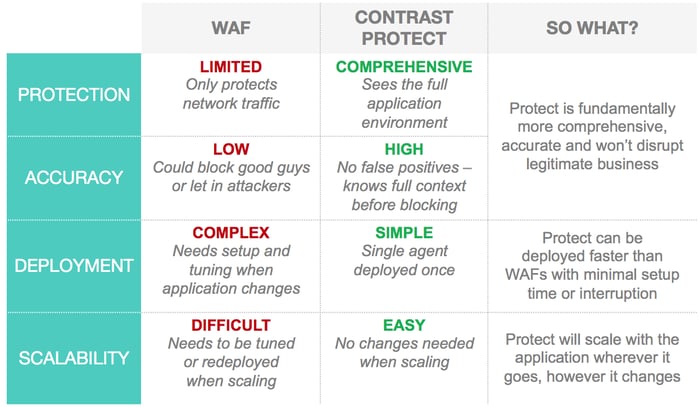
Contrast Protect helps to secure software applications in a radically better way than legacy tools like web application firewalls (WAFs). Contrast operates from within your application, moving and scaling with the app, providing accurate attack visibility, monitoring and protection because it is fully aware of the running application.
PINPOINT APP ATTACKS
Down to the Exact Line of Code
A WAF can’t tell you the line of code that is being attacked, but Contrast Protect can. Unlike WAFs or external scanners, Contrast analyzes and protects applications from within by integrating security safeguards into the running application making it self-protecting.
Most WAFs use signatures or regular expressions as the decision engine to detect and block attacks. Contrast Protect analyzes how the application treats the network traffic to understand an attack's true impact. Therefore, Protect’s decision to alert or block is based on facts gathered in real time. WAF decisions are, on the other hand, predictions.
Table 1: How Contrast Protect compares to a WAF.
SPEED
Immediately block known exploits.
Virtually patch newly discovered vulnerabilities.
Contrast Protect becomes an essential part of the application, making attack protection nimble and quick, shrinking the time from “vulnerable” to “protected” even from zero day attacks. Sure, Contrast not only blocks known attacks like SQL Injection, Cross Site Scripting (XSS), Command Injection, Path Traversal, CSRF, XML External Entity Processing (XXE), Java Deserialization and defends against bots… but also Contrast Protect can patch virtually, buying developers precious time until they can fix the issue(s) in the code. Here's a real-world example:
On March 6, 2017, a flaw was discovered in the widely used Apache Struts 2* frameworks. The next day, an exploit was announced, which allowed attacks to take control of Web servers.
Within hours of the announcement, Contrast Protect customers were able to defend their entire portfolio by applying a virtual patch. Within days, Contrast released a robust CVE Shield, which now automatically provides protection to all Protect customers..
Most of the tools available to secure software applications (SAST, DAST, and WAF) were invented over a decade ago… and their legacy underlying core technology prevents them from evolving to keep up with modern software movements like Agile and DevOps. With Contrast, software becomes self-protecting. Teams can analyze real-time security data from within the application, enabling them to monitor and block attacks.
* If you haven't addressed that Struts 2 vulnerability, you might want to push that "to do" up your priority list. According to our CTO & co-founder, Jeff Williams, Contrast is still under attack, but is entirely protected. Here is post he did a few weeks ago when he shared this information the first time.