Contrast Security has introduced a new report series, “State of Application Security,” based on research efforts by Contrast Labs. The data for these studies was gathered directly and continuously from within running applications and APIs using Contrast’s security analysis and protection platform. We’re excited to kick off the series with this Summer 2017’s State of Application Security: Libraries & Software Composition Analysis Report.
State of Application Security: Libraries & Software Composition Analysis Report
Think of an iceberg, a common analogy for application security where custom code is just the tip of the iceberg. Based on the this Contrast report, libraries constitute the largest percentage of application source code (79%).
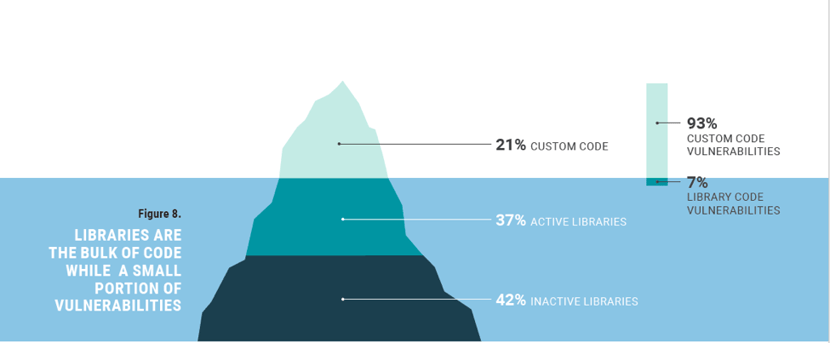
Surprisingly, Contrast Labs found data that does not reflect this common iceberg view of applications. When looking closer at an application’s codebase, the largest segment (42%) represents libraries with classes that are never called; this is defined as inactive libraries.
This means the common “iceberg” view of applications – with the vast majority of code being libraries – doesn’t reflect that most libraries actually represent inactive code.
Indeed, the iceberg analogy serves application security well when observing the relationship between custom code and libraries. However, after taking a deep dive into the Contrast Labs' data, an iceberg may not reflect where security teams should spend their efforts.
Only 7% of an application’s vulnerabilities are found in library code, with the majority of libraries left unused. This leads Contrast Labs to recommend focusing on remediating vulnerabilities within custom code.
Stay Updated
Be sure to subscribe to the blog to stay up to date on Contrast Labs' State of Application Security report series and other security thought leadership topics.